Google’s Threat Intelligence Group (GTIG) is warning that a “new and powerful” iOS exploit kit, dubbed Coruna by its developers, is being deployed on fake financial and cryptocurrency websites designed to redirect iPhone users to pages that can silently deliver exploits. For crypto holders, the risks are clear. According to GTIG’s analysis, the campaign ultimately focused on collecting seed phrases and wallet data from popular mobile apps.
Coruna targets Apple devices running iOS 13.0 to iOS 17.2.1 and comes bundled with 5 complete exploit chains and 23 exploits. GTIG said it recovered the kit after tracking its evolution over 2025, from initial use by a commercial monitoring company customer, to a “watering hole” attack on a compromised Ukrainian website, and ultimately to mass distribution via a Chinese-language fraudulent site tied to financially motivated attackers, which it tracks as UNC6691.
Crypto lures designed for iPhone
GTIG said it observed the JavaScript framework behind Coruna being deployed across a “very large” set of fake Chinese websites, primarily financial themed, during the fraud wave. One example cited by GTIG is a fake WEEX-branded cryptocurrency exchange page that attempts to push visitors onto iOS devices. A hidden iFrame is then inserted to deliver the exploit kit “regardless of geolocation.”
Related books
Delivery mechanisms are important because the line between traditional phishing and full device compromise is blurred. In GTIG’s story, simply landing on a compromised iPhone from a compromised iPhone was enough to start the chain. The framework fingerprints the device to determine its model and iOS version, and loads the appropriate WebKit remote code execution exploit and pointer authentication (PAC) bypass.
GTIG associated one recovered WebKit RCE with CVE-2024-23222, which Apple addressed in iOS 17.3 on January 22, 2024.
GTIG explains that Coruna introduces a stager it calls PlasmaLoader (tracked as PLASMAGRID) at the end of the chain, with a focus on financial information theft rather than traditional surveillance functions. According to GTIG, the payload can decode QR codes from images stored on the device and steal keywords such as “backup phrase” and “bank account” contained in Apple Notes by scanning text blobs for BIP39 word sequences.
Related books
The payload is also modular. According to GTIG, additional modules can be pulled down and executed remotely, and many of the identified modules are designed to hook into the functionality of popular cryptocurrency wallet apps (among them MetaMask, Trust Wallet, Uniswap wallets, and TON ecosystem wallets such as Phantom, Exodus, and Tonkeeper) to extract sensitive information.
Mobile security company iVerify has also warned of this broader issue, releasing its own findings around the same time as GTIG’s report. “And that’s exactly what happened here with mobile devices. Mobile phone OEMs are doing a better job than anyone else…”
What Cryptocurrency Users Can Do Now
Google says Coruna is “not effective on the latest versions of iOS” and urges users to update. If an update is not possible, GTIG recommends enabling Apple’s Lockdown Mode. GTIG also said it added the identified websites and domains to Google Safe Browsing to reduce further exposure.
For crypto-native users, the immediate benefit is that mobile wallets sit at the intersection of high-value assets and high-frequency web traffic, making “visit-to-compromise” campaigns pose a unique risk. According to the GTIG report, the fraud funnel was aimed not only at getting victims to connect their wallets, but also at directing them to the right device, right iOS version, so the rest could be exploited.
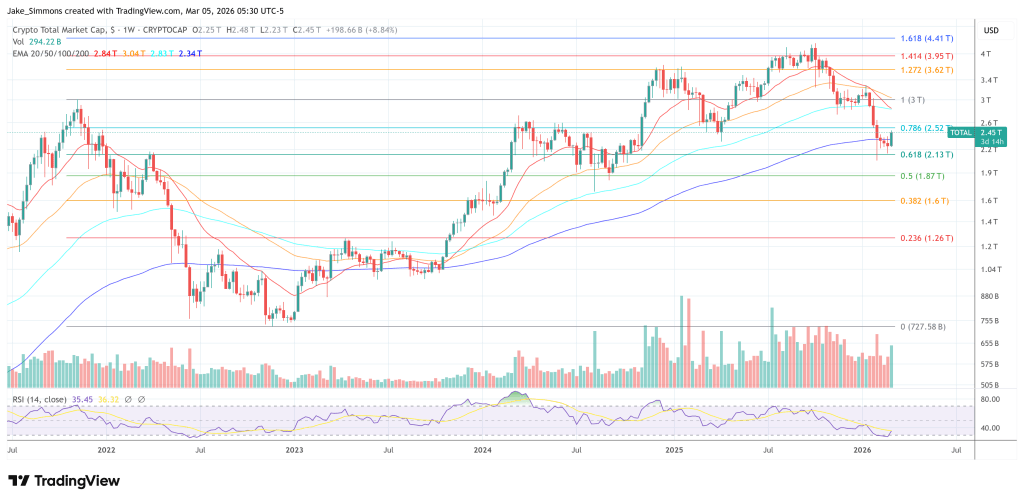
At the time of writing, the market capitalization of cryptocurrencies was $2.45 trillion.
Featured image created with DALL.E, chart on TradingView.com



